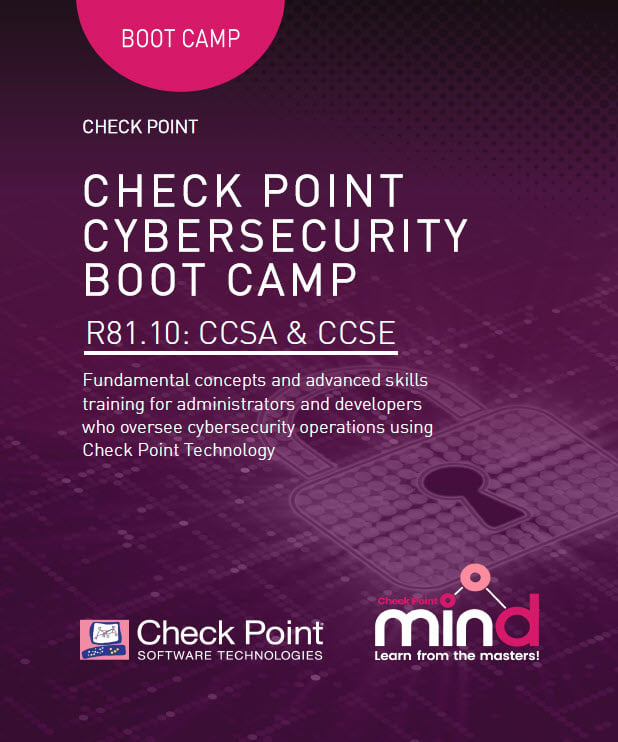
CheckPoint CCSA CCSE Bootcamp (CCSA-CCSE-Bootcamp) R81.10 – Fast Track Training for 5 days
About this Course
-
- Save 20% on your CCSA + CCSE Certification with this Fast Track Bundled Offer.
- Five-day course covers everything you need to start-up, configure and manage daily operations of Check Point Security Gateway and Management Software Blades systems on the GAiA operating system.
- Advanced course teaches how to build, modify, deploy and troubleshoot Check Point Security Systems on the GAiA operating system. Hands-on lab exercises teach h ow to debug firewall processes, optimize VPN performance and upgrade Management Servers. Validate and enhance your skills and optimally manage Check Point advanced security management systems.
Course Goals/Skills
- Know how to perform periodic administrator tasks
• Describe the basic functions of the Gaia operating system
• Recognize SmartConsole features, functions, and tools .
• Describe the Check Point Firewall infrastructure
• Understand how SmartConsole is used by administrators to grant permissions and user access
• Learn how Check Point security solutions and products work and how they protect networks
• Understand licensing and contract requirements for Check Point security products
• Describe the essential elements of a Security Policy
• Understand the Check Point policy layer concept
• Understand how to enable the Application Control and URL Filtering software blades to block access to various applications
• Describe how to configure manual and automatic NAT
• Identify tools designed to monitor data, determine threats and recognize opportunities for performance improvements
• Identify SmartEvent components used to store network activity logs and identify events
• Know how Site-to-Site and Remote Access VPN deployments and communities work
• Explain the basic concepts of ClusterXL technology and its advantages - Articulate Gaia system management procedures.
• Explain how to perform database migration procedures.
• Articulate the purpose and function of Management High Availability.
• Describe how to use Check Point API tools to perform management functions.
• Articulate an understanding of Security Gateway cluster upgrade methods.
• Discuss the process of Stateful Traffic inspection.
• Articulate an understanding of the Check Point Firewall processes and debug procedures.
• Describe advanced ClusterXL functions and deployment options.
• Explain how the SecureXL acceleration technology enhances and optimizes Security Gateway performance.
• Describe how the CoreXL acceleration technology enhances and improves Security Gateway performance.
• Articulate how utilizing multiple traffic queues can make traffic handling more efficient.
• Describe different Check Point Threat Prevention solutions for network attacks.
• Explain how SandBlast, Threat Emulation, and Threat Extraction help to prevent security incidents.
• Recognize alternative Check Point Site-to-Site deployment options.
• Recognize Check Point Remote Access solutions and how they differ from each other.
• Describe Mobile Access deployment options.
Intended Audience
- Technical professionals who need to deploy and manage Endpoint Security within their security environment.
Course Format

Language: English or Bulgarian
Course Materials:Digital Format. Lifetime Access. Official Learning Material from Check Point.
Lab: Individual Environment for each Delegate.
Course Duration
- 5 working days (09:00 – 17:00 / 9:00 am – 5:00 pm) UTC +2 (contact us for another Time Zone)
or
- 40 learning hours after hours (2 weeks, classes are held 4 times a week in one of the following options):
- Sat. and Sun. 10:00 – 14:00 or 14:00 – 18:00 or 18:00 – 22:00
- Mon. and Wed. 19:00 – 23:00
- Tue. or Thu. 19:00 – 23:00
Payments
You can enroll with your Check Point Learning Credits.
If you are Check Point Partner you can also get free training via the Co-op Program. Check your eligibility and request funds here or For any further questions or additional assistance, please E-Mail: [email protected]
We provide Invoices for Company Sponsored Trainings.
Invoices can be requested up to 7 days after the payment.
Course Schedules
Other Check Point Classes
If you dont see a date, contact us.
All classes are confirmed individually after enrollment.
Course Prerequisites
-
-
- Basic knowledge of networking
- 6 months to 1 year of experience with Check Point products recommended
-
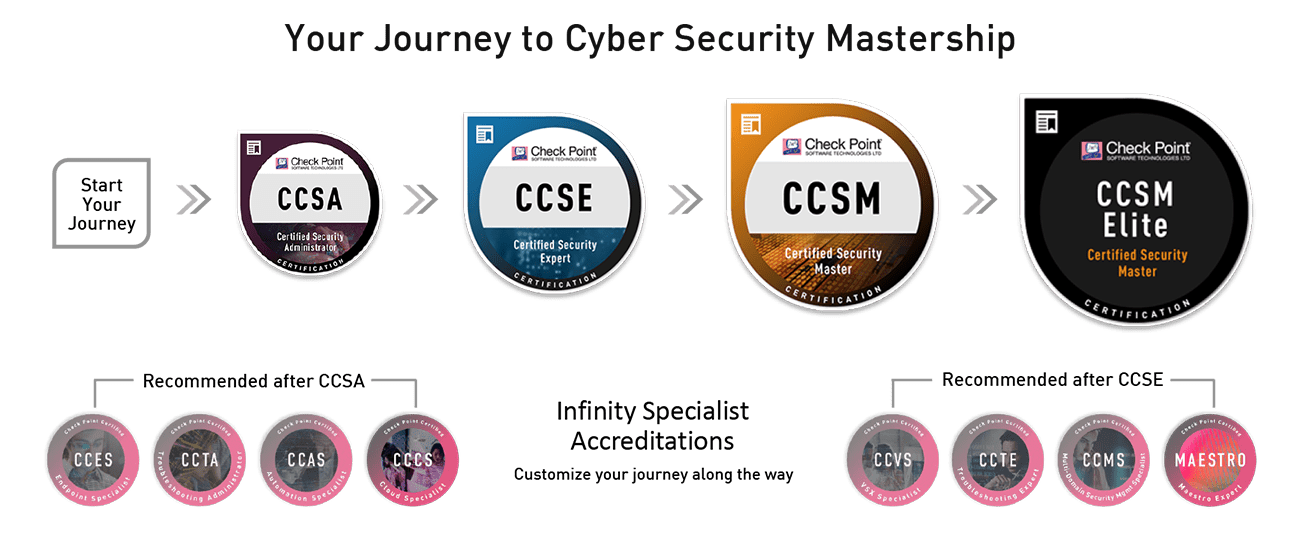
This Training will Prepare you to take the following Certification Exams (exam price included)
- Check Point Certified Security Admin (CCSA) R81.x
- Check Point Certified Security Expert (CCSE) R81.x
- You can Certify Online or at our Test Center.
Course Objectives:
• Identify key components and configurations
• Create and confirm administrator users for the domain
• Validate existing licenses for products installed on your network
• Create and modify Check Point Rule Base objects
• Demonstrate how to share a layer between Security Policies
• Analyze network traffic and use traffic visibility tools
• Monitor Management Server States using SmartConsole
• Demonstrate how to run specific SmartEvent reports
• Configure a SmartEvent server to monitor relevant patterns
• Configure and deploy a site-to-site VPN
• Configure and test ClusterXL with a High Availability configuration
• Understand how to use CPView to gather gateway information
• Perform periodic tasks as specified in administrator job descriptions
• Test VPN connection and analyze the tunnel traffic
• Demonstrate how to create custom reports
• Demonstrate how to configure event Alerts in SmartEvent
• Utilize various traffic visibility tools to maintain Check Point logs
Perform an upgrade of a Security Management server in a distributed environment.
Use the migrate_export command to prepare to migrate a Security Management Server.
Deploy a Secondary Management Server.
Demonstrate how to define new network and group objects using the Check Point API.
Perform an upgrade of Security Gateways in a clustered environment.
Use Kernel table commands to evaluate the condition of a Security Gateway.
Use common commands to evaluate the condition of a Security Gateway.
Configure Virtual MAC.
Demonstrate how SecureXL affects traffic flow.
Describe how the CoreXL acceleration technology enhances and improves Security Gateway performance.
Demonstrate how to monitor and adjust interface traffic queues.
Identify specific threat protections used by Check Point Threat Prevention.
Demonstrate how to enable Mobile Access for remote users.